..because it doesn’t have enough privileges to do so! Starting from Windows 8.1, Protected Process Light (PPL) was introduced. Protected Processes were implemented in Windows Vista (and was mostly focused on DRM), but it was greatly improved, such has having different levels of protection, depending on the application.
There are multiple uses of PPL, but for this post, let’s focus on Antivirus software. We’ll also not be diving deep into how to develop this. If you’re developing this, you probably know far more than me and this blog.
Since Antivirus (AV) software are at the forefront of stopping viruses from harming machines, it’s a very common target for viruses. Normally, AVs place a lot of rules and heuristics inside the application to protect against such threats, but PPL now enables antivirus software to run as a Protected Application under the PPL scheme.
There are multiple levels under the PPL Scheme: from 0 to 7. 0 is no protection and 7 is maximum protection. The kernel is protected under level 7, critical windows components are level 6 and antiviruses run at level 3. Processes with a higher level have more power and will trump over lower levels in terms of accessibility. So, an antivirus cannot terminate a critical windows process, since level 6 is higher than level 3.
Not all Windows Components are protected under the PPL scheme, critical applications such as ssms.exe, csrss.exe, services.exe are under the PPL scheme, running at level 6. Applications such as Task Manager is not under the PPL scheme, and for a very valid reason.
The PPL scheme allows such AVs services to be launched and protected from unloaded untrusted code. Given that an AVs have the PPL value of PROTECTION_LEVEL_CODEGEN_LIGHT (https://docs.microsoft.com/en-us/windows/win32/api/processthreadsapi/ns-processthreadsapi-process_protection_level_information), all DLLs that it loads needs to have a equivalent DLL Signature Level or higher. This ensures that no DLL foul play, such as file replacement or plating takes place. These checks are done at DLL loading level by the Code Integrity Windows component.
If you’re looking to create an application under the PPL scheme, you’ll need to get it signed by Microsoft. Given that only Microsoft can sign applications to contain these kinds of protection levels, viruses can’t have this kind of protection. Keeping in mind that PPLs run more privileged to non-protected processes (even those applications running as Admin), viruses simply cannot terminate AV processes.
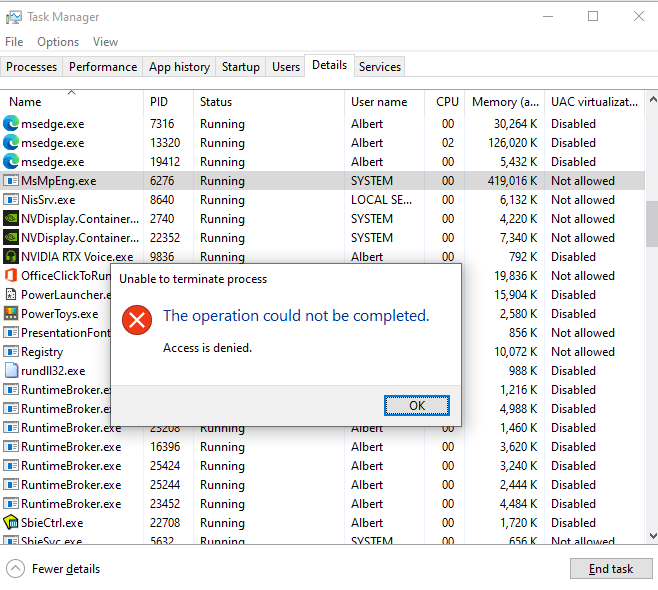
You can see this for yourself – fire up Task Manager (even if admin mode if you’d like) and try to close MsMpEng.exe (Windows Defender Service). If you try to terminate the process, Task Manager will just say “Access Denied”. This is because since Task Manager is not under the PPL scheme, it simply doesn’t have enough rights terminate the AV.
You can read a bit more on how AVs are protected here: https://docs.microsoft.com/en-us/windows/win32/services/protecting-anti-malware-services-
